Premesso che sui server che gestisco gli attacchi di tipo bruteforce sono all’ordine del giorno, oggi fail2ban ha cominciato ad imprecare in modo alquanto insistente.
Ma cosa ci sarà da strillare così tanto? Do un’occhiata ai file di log e mi accorgo che da ben 12 ore, un certo indirizzo IP sta provando a forzare il servizio SSH in ascolto sulle mie macchine.
Uhm, vediamo un po’ cosa dice il mio amico fail2ban:
Hi, The IP 174.132.*.* has just been banned by Fail2Ban after 6 attempts against ssh. Here are more information about 174.132.*.*: # # Query terms are ambiguous. The query is assumed to be: # "n 174.132.*.*" # # Use "?" to get help. # # # The following results may also be obtained via: # http://whois.arin.net/rest/nets;q=174.132.*.*?showDetails=true&showARIN=false # NetRange: 174.132.0.0 - 174.133.255.255 CIDR: 174.132.0.0/15 OriginAS: AS36420, AS30315, AS13749, AS21844 NetName: NETBLK-THEPLANET-BLK-15 NetHandle: NET-174-132-0-0-1 Parent: NET-174-0-0-0-0 NetType: Direct Allocation RegDate: 2008-06-17 Updated: 2008-06-17 Ref: http://whois.arin.net/rest/net/NET-174-132-0-0-1 OrgName: ThePlanet.com Internet Services, Inc. OrgId: TPCM Address: 315 Capitol Address: Suite 205 City: Houston StateProv: TX PostalCode: 77002 Country: US RegDate: 1999-08-31 Updated: 2010-10-13 Ref: http://whois.arin.net/rest/org/TPCM ReferralServer: rwhois://rwhois.theplanet.com:4321 OrgNOCHandle: THEPL-ARIN OrgNOCName: The Planet NOC OrgNOCPhone: +1-281-822-4204 OrgNOCEmail: noc@theplanet.com OrgNOCRef: http://whois.arin.net/rest/poc/THEPL-ARIN OrgTechHandle: TECHN33-ARIN OrgTechName: Technical Support OrgTechPhone: +1-214-782-7800 OrgTechEmail: admins@theplanet.com OrgTechRef: http://whois.arin.net/rest/poc/TECHN33-ARIN OrgAbuseHandle: ABUSE271-ARIN OrgAbuseName: The Planet Abuse OrgAbusePhone: +1-281-714-3560 OrgAbuseEmail: abuse@theplanet.com OrgAbuseRef: http://whois.arin.net/rest/poc/ABUSE271-ARIN RTechHandle: TECHN33-ARIN RTechName: Technical Support RTechPhone: +1-214-782-7800 RTechEmail: admins@theplanet.com RTechRef: http://whois.arin.net/rest/poc/TECHN33-ARIN RAbuseHandle: ABUSE271-ARIN RAbuseName: The Planet Abuse RAbusePhone: +1-281-714-3560 RAbuseEmail: abuse@theplanet.com RAbuseRef: http://whois.arin.net/rest/poc/ABUSE271-ARIN RNOCHandle: THEPL-ARIN RNOCName: The Planet NOC RNOCPhone: +1-281-822-4204 RNOCEmail: noc@theplanet.com RNOCRef: http://whois.arin.net/rest/poc/THEPL-ARIN # # ARIN WHOIS data and services are subject to the Terms of Use # available at: https://www.arin.net/whois_tou.html # Found a referral to rwhois.theplanet.com:4321. %rwhois V-1.5:003eff:00 whois.theplanet.com (by Network Solutions, Inc. V-1.5.9.5) Network:Class-Name:network network:ID:NETBLK-THEPLANET-BLK-15 network:Auth-Area:174.132.0.0/15 network:Network-Name:TPIS-BLK-174-132-*-0 network:IP-Network:174.132.*.*/29 network:IP-Network-Block:174.132.*.* - 174.132.*.* network:Organization-Name:Mike Dillard network:Organization-City:Austin network:Organization-State:TX network:Organization-Zip:78701 network:Organization-Country:USA network:Description-Usage:customer network:Server-Pri:ns1.theplanet.com network:Server-Sec:ns2.theplanet.com network:Tech-Contact;I:abuse@theplanet.com network:Admin-Contact;I:abuse@theplanet.com network:Created:20090204 network:Updated:20090216 %ok Regards, Fail2Ban
Ah che bello… finalmente un attacco che non proviene dal classico cinese smanettone. Ehm, però qui c’è qualcosa che non mi quadra (leggasi server farm), proviamo a fare un piccolo nmap su quell’indirizzo, va:
nightfly@nightbox:~$ sudo proxychains nmap -sS 174.132.*.* [sudo] password for nightfly: ProxyChains-3.1 (http://proxychains.sf.net) Starting Nmap 5.00 ( http://nmap.org ) at 2011-04-12 20:20 CEST Interesting ports on **.ae.**ae.static.theplanet.com (174.132.*.*): Not shown: 983 closed ports PORT STATE SERVICE 21/tcp open ftp 22/tcp open ssh 25/tcp open smtp 53/tcp open domain 80/tcp open http 106/tcp open pop3pw 110/tcp open pop3 111/tcp open rpcbind 143/tcp open imap 443/tcp open https 465/tcp open smtps 993/tcp open imaps 995/tcp open pop3s 1040/tcp open netsaint 1311/tcp open rxmon 3306/tcp open mysql 8443/tcp open https-alt
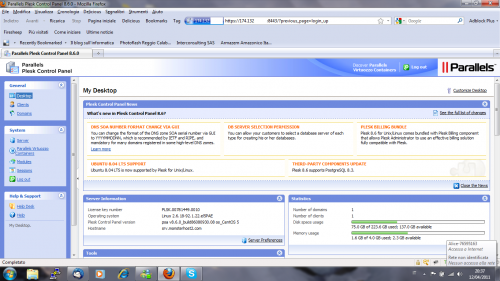
Ecco, c’è solo qualche servizio in ascolto… e tra questi vi è anche il mitico Plesk! Chissà cosa accadrebbe se…
Bye.
SSH Bombingultima modifica: 2011-04-14T09:51:00+02:00da
Reposta per primo quest’articolo
Complimenti per i tuoi articoli! Credo che ti seguirò più spesso. Se ti interessa uno scambio link Amici fammi sapere.
Ciao
Ciao Mattia,
grazie per i complimenti.
Puoi mandarmi il tuo link all’indirizzo che trovi scritto sul CV.